Why and how to conduct an OT security assessment ?
This guide details all the critical step to conduct an effective OT security assessment. Leveraging the ISA 63443 Standard the methodology.

This guide details all the critical step to conduct an effective OT security assessment. Leveraging the ISA 63443 Standard the methodology.
In the interconnected world of industrial automation the importance of PLC data is paramount and should be leverage !
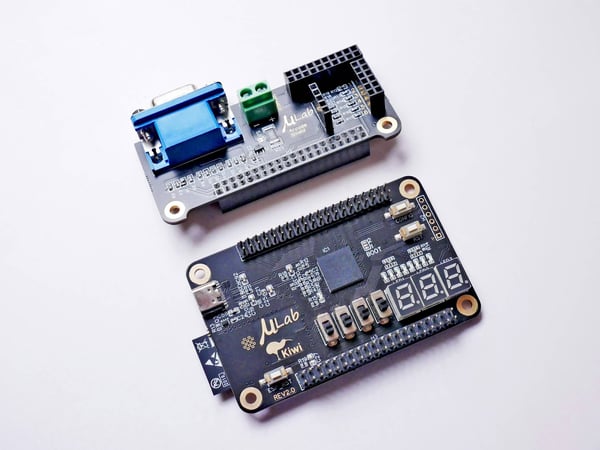
A Programmable Logic Controller (PLC) is a digital computer used in industrial automation to monitor, control, and automate various processes and...

Explore the comprehensive guide to CIS Controls V8. Get detailed analyses of the latest updates and all 18 controls for robust cybersecurity.
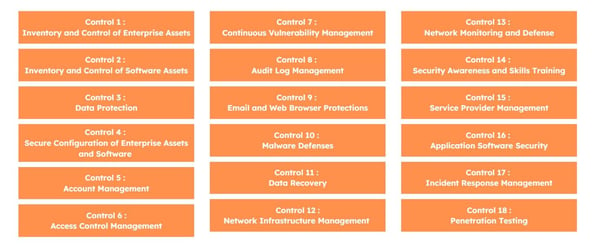
Explore the comprehensive guide to CIS Controls V8. Get detailed analyses of the latest updates and all 18 controls for robust cybersecurity.

Discover the power of log analytics : Streamlined Troubleshooting, Strengthened Security Monitoring, Optimized Performance and make Data-Driven...
Discover the ISO 27001 new controls, they are 11, and have been implemented in October 2022. Implement these 11 new controls before your next audit !
Detailed explanation about the latest changes about ISO-27001-2022 controls : 11 new controls, 4 categories instead of 14 and introduction of 5...

Understand what is a cybersecurity playbook, what are the differents functions of it and what are the differents types of playbooks. Read Now !